In the realm of digital image processing, the concept of Pixel Value Differencing (PVD) stands out as a powerful technique for embedding data within images. This method, also known as the Pixel Value Differencing method, is particularly useful for steganography, the practice of hiding information within other data. By manipulating the differences between pixel values, PVD allows for the concealment of data in a way that is virtually undetectable to the human eye. This blog post delves into the intricacies of Pixel Value Differencing, its applications, and the steps involved in implementing this technique.
Understanding Pixel Value Differencing
Pixel Value Differencing is a steganographic technique that modifies the differences between adjacent pixel values to embed secret data. Unlike other methods that alter individual pixel values, PVD focuses on the differences between neighboring pixels, making it more resilient to detection and tampering. This approach ensures that the embedded data does not significantly alter the visual appearance of the image, preserving its integrity.
The basic idea behind PVD is to adjust the differences between pixel values in a way that encodes the secret message. For example, if the difference between two adjacent pixels is modified to encode a bit of the secret message, the overall image quality remains largely unchanged. This subtle manipulation is what makes PVD an effective tool for steganography.
Applications of Pixel Value Differencing
Pixel Value Differencing has a wide range of applications in various fields, including:
- Secure Communication: PVD can be used to embed secret messages within images, allowing for secure communication over insecure channels.
- Digital Watermarking: By embedding a watermark within an image, PVD can help protect digital content from unauthorized use and distribution.
- Data Hiding: PVD can be employed to hide sensitive information within images, ensuring that it remains concealed from unauthorized access.
- Image Authentication: By embedding authentication data within an image, PVD can help verify the authenticity and integrity of digital images.
Steps Involved in Pixel Value Differencing
The process of embedding data using Pixel Value Differencing involves several key steps. These steps include preparing the image, calculating pixel differences, embedding the secret data, and reconstructing the image. Below is a detailed explanation of each step:
Preparing the Image
The first step in the PVD process is to prepare the image for data embedding. This involves selecting an image that will serve as the carrier for the secret data. The image should be in a format that supports pixel-level manipulation, such as BMP or PNG. Additionally, the image should be of sufficient quality to ensure that the embedded data does not significantly alter its appearance.
Calculating Pixel Differences
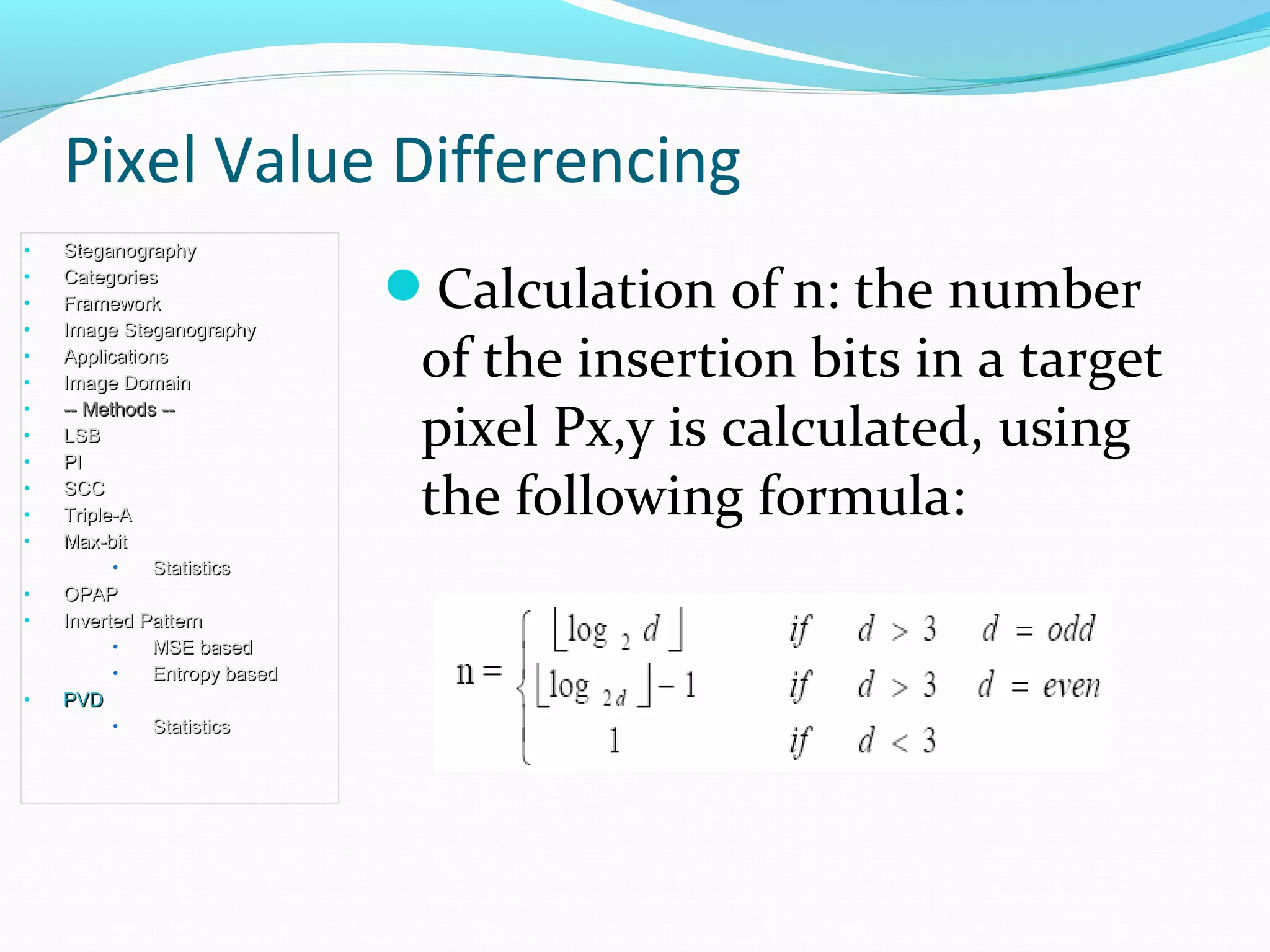
Once the image is prepared, the next step is to calculate the differences between adjacent pixel values. This is done by iterating through the image and computing the difference between each pair of neighboring pixels. The differences are then stored in an array for later use.
For example, if the pixel values of two adjacent pixels are A and B, the difference can be calculated as:
Difference = |A - B|
Embedding the Secret Data
After calculating the pixel differences, the secret data can be embedded within the image. This is done by modifying the differences to encode the bits of the secret message. The modification is typically done in a way that minimizes the visual impact on the image. For example, if the secret message bit is 1, the difference may be increased by a small amount, and if the bit is 0, the difference may be decreased by a small amount.
The embedding process can be summarized as follows:
- Iterate through the array of pixel differences.
- For each difference, modify it based on the corresponding bit of the secret message.
- Update the pixel values in the image to reflect the modified differences.
Reconstructing the Image
Once the secret data is embedded, the final step is to reconstruct the image. This involves updating the pixel values in the image to reflect the modified differences. The reconstructed image should appear virtually identical to the original image, with the secret data concealed within it.
It is important to note that the reconstruction process should be reversible, allowing the secret data to be extracted from the image at a later time. This ensures that the embedded data can be retrieved when needed, without altering the image.
🔍 Note: The effectiveness of the PVD technique depends on the quality of the image and the amount of data being embedded. Higher-quality images can accommodate more data without significant visual degradation.
Extracting Data Using Pixel Value Differencing
To extract the secret data from an image that has been encoded using Pixel Value Differencing, the process involves reversing the steps used for embedding. This includes calculating the modified pixel differences, decoding the secret message, and reconstructing the original image. Below is a detailed explanation of the extraction process:
Calculating Modified Pixel Differences
The first step in extracting the secret data is to calculate the modified pixel differences in the image. This is done by iterating through the image and computing the differences between each pair of neighboring pixels, just as was done during the embedding process.
Decoding the Secret Message
Once the modified pixel differences are calculated, the next step is to decode the secret message. This is done by interpreting the differences to extract the bits of the secret message. For example, if a difference has been increased, it may correspond to a bit value of 1, and if it has been decreased, it may correspond to a bit value of 0.
The decoding process can be summarized as follows:
- Iterate through the array of modified pixel differences.
- For each difference, decode the corresponding bit of the secret message.
- Reconstruct the secret message from the decoded bits.
Reconstructing the Original Image
After extracting the secret data, the final step is to reconstruct the original image. This involves updating the pixel values in the image to reflect the original differences, before the secret data was embedded. The reconstructed image should appear virtually identical to the original image, with the secret data removed.
It is important to note that the reconstruction process should be reversible, allowing the original image to be restored without any loss of quality. This ensures that the image can be used for its intended purpose, even after the secret data has been extracted.
🔍 Note: The extraction process should be performed carefully to ensure that the secret data is accurately decoded and the original image is correctly reconstructed. Any errors in the process can result in data loss or image degradation.
Advantages and Limitations of Pixel Value Differencing
Pixel Value Differencing offers several advantages as a steganographic technique, but it also has its limitations. Understanding these aspects is crucial for effectively implementing PVD in various applications.
Advantages
- High Capacity: PVD can embed a large amount of data within an image without significantly altering its appearance.
- Low Detectability: The technique is difficult to detect, as it modifies the differences between pixel values rather than the values themselves.
- Robustness: PVD is resilient to common image processing operations, such as compression and noise addition.
- Reversibility: The embedding and extraction processes are reversible, allowing the original image and secret data to be accurately reconstructed.
Limitations
- Image Quality: The effectiveness of PVD depends on the quality of the image. Lower-quality images may not be able to accommodate as much data without visible degradation.
- Complexity: The implementation of PVD can be complex, requiring careful calculation and manipulation of pixel differences.
- Sensitivity to Attacks: While PVD is robust to common image processing operations, it may be vulnerable to more sophisticated attacks designed to detect and remove hidden data.
Comparing Pixel Value Differencing with Other Steganographic Techniques
Pixel Value Differencing is just one of many steganographic techniques available for embedding data within images. Other popular methods include Least Significant Bit (LSB) encoding, Discrete Cosine Transform (DCT) based steganography, and Spread Spectrum Image Steganography. Each of these techniques has its own strengths and weaknesses, making them suitable for different applications.
Here is a comparison of PVD with some of the other commonly used steganographic techniques:
| Technique | Capacity | Detectability | Robustness | Complexity |
|---|---|---|---|---|
| Pixel Value Differencing | High | Low | High | Moderate |
| Least Significant Bit (LSB) | Moderate | Moderate | Low | Low |
| Discrete Cosine Transform (DCT) | High | Low | High | High |
| Spread Spectrum Image Steganography | Low | Very Low | Very High | Very High |
As shown in the table, Pixel Value Differencing offers a good balance of capacity, detectability, robustness, and complexity. While it may not be the best choice for all applications, it is a versatile technique that can be effectively used in a wide range of scenarios.
🔍 Note: The choice of steganographic technique depends on the specific requirements of the application, including the amount of data to be embedded, the desired level of detectability, and the robustness to various attacks.
Future Directions in Pixel Value Differencing
The field of steganography is continually evolving, with new techniques and improvements being developed to enhance the effectiveness and security of data hiding. Pixel Value Differencing is no exception, and there are several areas where future research and development can focus:
- Improved Algorithms: Developing more efficient algorithms for calculating and modifying pixel differences can enhance the capacity and robustness of PVD.
- Advanced Detection Methods: Creating advanced detection methods to identify and remove hidden data can help improve the security of PVD.
- Integration with Other Techniques: Combining PVD with other steganographic techniques can create hybrid methods that offer enhanced security and capacity.
- Real-Time Applications: Developing real-time applications for PVD can enable its use in scenarios where immediate data embedding and extraction are required.
By addressing these areas, researchers and developers can continue to advance the field of steganography and make Pixel Value Differencing an even more powerful tool for secure communication and data hiding.
In conclusion, Pixel Value Differencing is a robust and versatile steganographic technique that offers numerous advantages for embedding data within images. By understanding the principles behind PVD, its applications, and the steps involved in implementing this technique, one can effectively use it for secure communication, digital watermarking, data hiding, and image authentication. While PVD has its limitations, ongoing research and development can help overcome these challenges and enhance its effectiveness in various applications. As the field of steganography continues to evolve, Pixel Value Differencing will remain a valuable tool for those seeking to conceal information within digital images.